On the recent episode of "Who Wants to Be a Millionaire ?", there was a neat little question that Günther Jauch clearly had to think about: "A number is always divisible by \(4\) without a remainder if the number formed from its last two digits is...?" – and this is precisely where you have to think mathematically for a moment, instead of being lured by the pretty distractions. Because while answers like "is even", "contains a \(0\) , or "the sum of the digits is \(4\) " sound plausible at first glance, the correct answer lies in a simple property of our decimal system.
...Some mathematical problems are formulated so simply that they can be explained to a child, yet so difficult that they occupy generations of mathematicians. One such problem is the so-called unit distance problem: Place \(n\) points in the plane. How many pairs of points can then have a distance of exactly \(1\) ? The problem dates back to Paul Erdős and has been studied since 1946. OpenAI has now published that an internal model has disproven a long-held conjecture about this problem.
...In October 1999, a group led by the then 16-year-old Norwegian Jon Lech Johansen released the DeCSS program to circumvent the Content Scramble System (CSS) DVD playback protection. CSS used 40-bit encryption, the keys to which were distributed to licensed manufacturers, to restrict DVD playback. Because the distribution of the code fell under the US DMCA and was legally prohibited, activists sought ways to disguise the code as a mathematical entity.
...The rational numbers \(\mathbb{Q}\) appear at first glance to be a continuous whole: between any two fractions, there is always another. But this impression is deceptive: there are sets of rational numbers that are indeed bounded, but whose supremum or infimum simply does not exist in \(\mathbb{Q}\) . The reason lies in the existence of irrational numbers like \(\sqrt{2}\) , which, in a sense, create invisible holes in the rational number line.
...PaperMC provides a simple foundation for extending Minecraft server-side with small plugins, without requiring clients to install anything. When developing plugins, the question arises of how to display dynamic information to the player. The answer lies in an often overlooked vanilla feature: the boss bar . Originally intended for end bosses, the boss bar can be repurposed and used as a minimalist HUD.
...The Internet Protocol (IP) is the foundation of all internet applications. Other protocols, such as TCP and UDP, build upon it, transporting services like HTTP(S), email, telephony, and DNS. IPv6 is replacing the outdated transport protocol IPv4 because its relatively small address space of around 4 billion addresses has long been exhausted. IPv6 is now almost ubiquitous and more useful than many realize.
...We've all been there: You need to quickly download something from a cheap shared hosting package (e.g., from IONOS). git pull You might want to run a program or use a database, but your hosting provider doesn't grant SSH access – or only in more expensive plans. Often, the only option left is the tedious process of manually uploading files via FTP, which makes deployments unnecessarily complicated and prone to errors.
Amazon is the perfect shopping channel for freelancers: fast, affordable, and everything in one place. Amazon has now managed to consistently provide timely and readily available invoices for download (even for purchases on the Marketplace). Whether it's a new laptop, an office chair, or just a quick order of printer paper – the goods can be ordered with just a few clicks, usually via the personal account that you've had for years anyway.
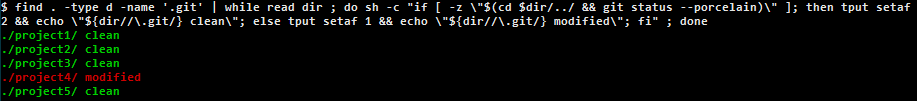
...Whoever is first in the morning git status Anyone who types and then drinks coffee will love this little helper. Especially when developing many web projects in parallel, a compact overview is invaluable: Where is the work tree clean, where are there unmerged changes, and where is a pull/push pending? A small shell tool is all you need – as long as it handles spaces/Unicode in paths robustly and doesn't choke on stuck remotes.
There's a beautiful song by Cali Rose called "It Is What It Is and It Ain't What Is Ain't ." This can be simplified to "It is what it is and it isn't what it isn't." With just a few words, entire worlds of truth can be explored. By varying and combining the two halves, a small playground for logic emerges. Now you can take this sentence and find other interesting examples.
...Thunderbird has experienced a remarkable revival since 2022. After years of stagnation, the Mozilla Foundation is once again actively investing in its development. The Supernova initiative (Thunderbird 115+) brought fundamental modernizations such as Rust integration for performance-critical components, a modernized UI based on Web Components, and native Exchange support via the EWS/Microsoft Graph API.
...In October 2019, Python 3.8 introduced the Walrus operator (:=) via PEP 572 – and thereby triggered one of the biggest controversies in the history of the programming language. The debate was so bitter that Python inventor Guido van Rossum in July 2018 – even before the release – his position as BDFL (Benevolent Dictator For Life). Since the beginning of 2019, Python has instead been governed by an elected Steering Council.
You're on the phone with a friend in the USA on a freezing cold winter day. "It's minus \(40\) degrees here!" you both exclaim simultaneously. Normally, this would be a matter of clarifying who means Celsius and who means Fahrenheit—but not at this particular temperature. Why is that? This point is the only temperature at which the Celsius and Fahrenheit scales agree!
...Most graphical file managers don't sort strictly lexicographically, but rather use "natural" sorting. Blocks of numbers in names are interpreted as numbers—the larger block of numbers wins, even if the opposite would be true alphabetically. The idea behind natural sorting: What people usually want is "9 before 10," "Chapter 2 before Chapter 10"—without having to add leading zeros.
...Anyone who runs jobs in the Windows Task Scheduler will sooner or later encounter inexplicable runtime differences. A PHP script that runs in 5 minutes on the command line suddenly takes 20 minutes when executed via the Windows Task Scheduler. Same user, same permissions, same code – four times the execution time. What was going on?
...The continuous decline in the price of computing power—two orders of magnitude per decade—has fueled deep learning models enormously since 2010. Larger networks plus more data seemingly reliably delivered ever-higher scores on common benchmarks—and fueled the hope that scaling alone would inevitably lead to AGI. As early as 2019, François Chollet introduced the ARC-AGI benchmark. to measure intelligence.
...The sender's email address remains a good indicator of whether an email is spam or not. By default, it's not intuitive in Microsoft Outlook Desktop to expand the view to include a column that displays the specific email address instead of the name. Microsoft hasn't yet implemented this feature as a simple option, but it can be added to the classic Windows version of Outlook using built-in tools.
...In times of HTTPS-only browsers, SameSite cookies, and realistic development conditions, it's important to work locally with genuine SSL certificates. Let's Encrypt has pioneered this approach – with the help of certbot and Cloudflare , creating and renewing wildcard certificates is quick and easy. This allows you to access your web projects encrypted on any device (smartphone, VM, etc.) on the local network or via VPN.
..."A machine can have a large memory, but it cannot think - unless we teach it." - Alan Turing. Modern AI models such as GPT-4 or Llama are based on huge data sets and complex mathematical structures. But what is really behind them? In this article, we look at the key components needed to build a language model from scratch.
...OpenStreetMap (OSM) is a free world map that is created jointly by people all over the world - free, open and independent. While Google Maps, as the market leader, is often the first choice for digital maps, OSM relies on a completely different principle: a collaborative community that collects, improves and makes geographical data available free of charge.
...Long announced - now reality : Microsoft has switched off authentication by password for certain protocols in Exchange Online from September 2022 in favor of oAuth2. The GitHub issues of many libraries and backup scripts make it clear that the changeover caught many administrators by surprise. Below we show a way how you can continue to access the contents of your Exchange mailbox with the help of oAuth2 via PHP via IMAP.
...Is the time inconvenient? Did you send your email too early? Delaying emails can be useful in many situations: whether it's to give yourself time to check something or to manage your own workload effectively - timing can be crucial. Here are three ways you can delay sending emails and optimize your own communication.
...Browser automation plays a big role in areas such as web scraping, automated testing, and web application interaction. Until now, Puppeteer, for example, has been used for this. With the advent of AI, new opportunities are now opening up to make browser automation more intuitive and less maintenance-intensive - making way for Stagehand .
...Xdebug is a powerful debugging and profiling tool for PHP that helps us analyze and optimize PHP applications. It supports features such as step-by-step debugging, performance measurement, and stack tracing, which makes debugging much easier and provides better insight into the code. Below is a small setup guide for using it within VSCode.
...Imagine two identical cups - one filled with coffee and the other with milk, both at the same level. A teaspoon of coffee is now scooped from the coffee cup into the milk cup and stirred. A teaspoon of the mixture from the milk cup is then poured back into the coffee cup. Which cup then contains more foreign liquid?
...Commit messages in Git are often neglected. Many see them merely as a necessary evil to save changes. Yet meaningful commit messages are a decisive factor for the success of a project: they ensure good traceability of changes, efficient team collaboration and faster troubleshooting. No reason to have the commit messages prepared automatically with the help of AI.
...February sometimes has an unusually appealing shape in the calendar. For example, in February 2021 you could experience such a moment, a "perfectly rectangular February". This rare effect occurs when February has exactly \(28\) days and February 1 falls on a Monday. But how often does this actually happen and how long do you have to wait for the next time?
...CSS is still confusing for most of us: it has hundreds of poorly named properties, each of which can affect the result in non-intuitive ways. Vertical positioning of elements in web development is tricky and has often been a headache in the past, but those days are thankfully over.
...CSS transitions are a good way to create interactivity., transition to the initial state of an element, and the browser animates the transition between the two states. Transitions for intrinsic element variables such as auto have been a problem for web developers for decades, and the only option was to calculate the height dynamically using JavaScript.
There is no \(n \in \mathbb{Z}^+\), so that \(0 < n < 1\).
...In 1950, physicists George Gamow and Marvin Stern noticed an interesting phenomenon: Gamow, who had an office on the second floor of a six-story building, noticed that five times out of six, the next incoming elevator went down even though it was going up. Stern, who worked on the fifth floor, observed the opposite.
...A quine program, or quine, is a program that prints its own source code when executed. A quine must not "step out of itself" by, for example, printing the contents of the file in which it is contained or using introspective capabilities to print its own representation. Instead, it must compute its own source code.
...Powerful tools such as logrotate make it much easier to rotate log or backup files. The files are rotated after a certain period of time or when they reach a certain size. If you do not have this tool available on a remote server and can only execute SSH commands remotely, you can help yourself with a small bash script that deletes old files and only sends one request.
...In the world of numbers, we often come across surprising patterns that can be both perplexing and enlightening. One such curiosity is Benford's law, also known as the law of the first digit. This mathematical phenomenon describes the frequency distribution of the first digits in many real-world data sets and offers interesting insights into the nature of numbers as they occur in our environment.
...I have two children and a son who was born on a Thursday. What is the probability that I have a daughter? Let's denote the days of the week with the numbers \(1, 2, ... , 7\) with \(1\ =\) Monday, \(2 =\) Tuesday and so on. Now we can define the event as "a boy was born on day \(n\) " as \(B_n\), and similarly for \(G_n\).
...Assuming that the number \(Y\) of all people who have ever been born and will be born at some point is limited, let \(x\) be your absolute position from the beginning of the list. Then \(0 < \frac{x}{Y} \leq 1\). We can now say with a probability of \(95\%\) that you are among the last \(95\%\) of all people ever born, i.e. \(0.05 < \frac{x}{Y} \leq 1\) and thus \(Y < \frac{x}{0.05} = \frac{100 \cdot x}{5} = 20 \cdot x\).
...The following sentence is known as the "drinker's paradox": "There is someone in the pub, so if he or she is drinking, everyone in the pub is drinking." It doesn't matter if that one person encourages others to drink or some other back door exists, as we'll see in a moment. It is a nice example from mathematical first order logic.
...A boy thinks of a number that is \(1\) , \(2\) or \(3\) and a girl is then only allowed to ask one question about that number. The boy can only answer " Yes ", " No ", or " I don't know" . Through a clever questioning, the girl manages to name the correct number that the boy was thinking of after the boy has answered her. What is your question?
...Imagine that one day you receive a mysterious package with no sender. Curious, you open the package and find a ring that you give to your daughter. Decades later, she is the one who can use a wormhole to send objects back in time. She does this with the ring that you once gave her, wrapped in a package that she addresses to you. The question is: where does the ring come from?
...As an alternative to the highly valued Travis CI , GitHub Actions has also been available for some time. As a continuous integration tool, it is very well integrated on the GitHub code platform and is now very stable. GitHub Actions are based on YAML configuration files placed in the repository where the workflow should run.
...In 1961 James and Stein published the paper Estimation with Quadratic Loss . Take normally distributed data with an unknown mean \(\mu\) and variance \(1\) . If you now choose a random value \(x\) from this data and have to estimate the mean \(\mu\) on the basis of this, intuitively \(x\) is a reasonable estimate for \(\mu\) (since a normal distribution is present, the randomly chosen \(x\) is probably near \(\mu\) ).
...UUIDs (Universally Unique Id entifiers) are 128-bit values that are used in databases, among other things, to uniquely identify table entries. They are represented as a hexadecimal string divided into five groups separated by hyphens (Example: 09fe49b3-4d2b-471c-ac04-36c9e706b85f). There is numerous Discussions about the advantages and disadvantages of UUIDs in databases - they are indispensable in distributed systems.
Sensitive data or too much memory consumption: There are good reasons to want to change the Git history. In this blog post , I explained how to purge files from Git history using BFG . A weak point of BFG is the lack of support for direct paths , so you cannot specifically remove files or folders in subfolders from the history. With that, it's time to look at alternative solutions.
...tl;dr: Manually set value or the default values of WP_MEMORY_LIMIT/WP_MAX_MEMORY_LIMIT have no effect if WP_MEMORY_LIMIT/WP_MAX_MEMORY_LIMIT less than or equal to the memory limit of PHP (hereinafter memory_limit called) is. They are used to set too low values of memory_limit dynamically to a recommended minimum.
If you embed a third-party iframe (like a widget), you can't access its content with either CSS or JavaScript (due to the so-called same-origin policy ). However, there is a very simple procedure for modifying any code (also in other files that are reloaded within the iframe). To do this, you route the URL through your own PHP proxy and modify the content as you wish.
...ANTON is one of the most popular learning apps for students in grades 1-10. Class. At first glance, the gamification aspect of acquiring coins ("coins") may seem strange to adults - but it noticeably multiplies the motivation, not only of my children. It even saves a small "cushion" of coins that you do n't touch.
...As is well known, the German IBAN consists of the country code (DE), a two-digit check digit (according to ISO 7064 ), the bank code (8-digit) and the account number (incl. sub-account number, 10-digit, missing digits are filled with leading zeros) and is therefore 22 -digit. To calculate the check digit, the so-called BBAN (bank code and account number) as well as the numeric country code \(1314\) for Germany and the check digit \(00\) ) are formed.
...At the last family evening, the game Dobble (in the Harry Potter Edition) was enthusiastically brought to the table by the children. After the 5th lost round (with no visible hit of my card with the playing card) I was told, to my astonishment, that every player can always find a hit in every round. But my disbelief was only acknowledged with further lost laps - the children were simply faster.
...You know: The expected time between two Bitcoin blocks is on average \(10\) minutes. Now you are making an important Bitcoin transaction and waiting eagerly to see if and when it appears in the next block:
e50bfacc95975a4e7545d83d8954645f
...In the RKI weekly report of 11.11.2021 it is listed on p. 22 that \(36\%\) the over 60-year-old corona patients in the intensive care unit were already fully vaccinated. In this age group, \(87\%\) completely vaccinated at this point in time (see p. 18).
...Finite decimal numbers are called decimal fractions, because they are a different representation for fractions with powers of ten in the denominator. So is:
$$\frac{z}{n} = \frac{q_1}{1} + \frac{q_2}{10} + \dots + \frac{q_k}{10^k}$$
with \(k \in \mathbb{N}\) and \(q_k\) the \(k-1\) -th place to the right after the comma.
...The use of nvm is recommended for quick installation and changing of node versions. If you want to explicitly specify the required node version in a project, you put a file called .nvmrc with the exact version number (eg "12.10.0") in the same folder as the package.json . If you now change to the folder, the following extension of the file ~ / .bash_profile for bash executes the command nvm use , which automatically sets this version:
fe497e1c7f9f1547263eb3bffe15f9f6
...Ever since responsive web design has existed, developers have been asking about the possibility of designing DOM elements based on their actual size and not on the size of the viewport in the browser (with the help of media queries ). In fact, container queries (initially element queries) are probably the most requested CSS function that browsers still don't have .
...Sensitive data such as passwords should be in .env files and, if possible, not end up in Git repositories. But it has probably happened to each of us at least once by mistake: Quickly published a nice Google Maps JS API script on GitHub Gists (as "public") without accidentally disguising our own private Maps API key.
...If you want to cut out an image with the help of an SVG, the use of the CSS property clip-path is recommended. The following script triggers bumpy barriers: The SVG can be saved with the help of Illustrator, you can specify the (relative or absolute) URL of an SVG (Chrome supports up to now natively only inline SVG) and the neckline is also completely responsive.
...With the help of the meta_query attribute in the powerful WordPress WP_Query class, posts can be filtered that have certain values in their meta fields. If you have created a multi-line meta field (eg with the help of Advanced Custom Fields ) and only want to find posts that contain a certain value in this field separated by line breaks, the REGEX world of MySQL is recommended.
...In a previous article I described how one can easily integrate animations from Adobe Animate into a website via the detour of an APNG export. There is also the native way via the HTML5 canvas export , but anyone who has already worked with it will find that it is stuck at all corners (insufficient responsive support, cumbersome integration into existing websites, no different frame rates per animation, etc.) .). The library adobe-animate-embed provides a remedy here.
...Normally, when integrating Google Maps, you work with the Maps JavaScript API , which requires an API key and can cause costs that should not be underestimated with higher access numbers. There are great alternatives such as mapbox or OpenStreetMap , but they do not yet achieve the variety of features offered by Google. Google itself also offers a way without an API key via the share function, which we can use for our purposes.
...The browser support for animated PNG files is now so good that animations created with Animate CC can be easily exported to APNG and then incorporated into a website in a simple <img> tag. This is a simple and good quality alternative to the publishing method in Animate CC, which generates JavaScript. The steps that you have to take are described below.
...If you want to add meta fields to the native WordPress search, for example, it is advisable to take a look at the fired filters . The posts_search hook is recommended so that pagination continues to work and future improvements in the search are not canceled out . With the help of the REGEXP and ExtractValue functions, the following code extends this search to include posts that contain one of the search words entered in all meta fields.
...Along with Xovi, the SISTRIX tool is the most widely used analysis program in Germany in the area of SEO. The visibility index has established itself as a quasi-standard for the visibility of a page in Google search. The parameters that are included in its calculation are, for example , explained here and here and here and here and here , but an exact calculation formula is not officially published. The following are the results of my six-month personal research, which do not claim to be complete or correct.
...When Kurt Gödel published his famous Incompleteness Theorems in 1931, it shook the foundations of mathematical logic: He refuted that all axioms that can be set up as a possible basis are inevitably incomplete in order to prove all statements about numbers - and destroyed that Hilbert's dream to prove the consistency of mathematical theory.
...Despite all data protection concerns, WhatsApp is still the German favorite messenger app. In addition to the special WhatsApp Business App , Facebook has also created an official interface, the WhatsApp Business API, to make it more interesting for companies. If you want to send WhatsApp messages programmatically from your web application, there are other ways as well.
...If you use elements such as overlays (which is the rule in times of GDPR actionism) and want to soften the area behind the overlay, for example, you often come across the problem of the stacking context . For example, if you have elements positioned absolutely or in a fixed position, they are suddenly displayed differently than without an applied filter. But there is a remedy.
...You don't have to use a powerful tool like Google Optimize for simple URL split tests, but you can also solve Apache via .htaccess. The following code snippet distributes https://vielhuber.de/test1.php (variant 1) and https://vielhuber.de/test2.php (variant 2) its visitors equally to both versions for the two pages. The randomization is based on the current server time.
...When notating function definitions with case distinction, we use curly braces. We will pursue the simple question of whether this representation can be eliminated and the function can be traced back to a notation that can do without it. For example, can the function
$$f: \mathbb{R} \to \mathbb{R}, f(x) = \left\{\begin{matrix} 42, & \text{falls } x = 0 \\ x, & \text{sonst} \end{matrix}\right.$$
with the help of the four basic arithmetic operations using a one-line term?
...When visualizing data in Google Sheets, one encounters the problem that the \(x\) axis cannot automatically fill in the missing gaps for text values (such as calendar weeks). To solve the problem, one generates a continuous date series, counts the occurring cells themselves and then visualizes the cumulated totals.
...As part of its Google Cloud, Google offers the Google Translation API with a usage-based cost structure. In addition, there is an undocumented API that can be used without a key, but which denies service after only a few requests. When using the website translation function of Google Chrome, it is noticeable that pages can be translated here in very good quality without any noticeable limitation.
...If you link Github with Composer , a version number must be assigned via git tag . The following command line command determines the current day and increases it (according to SemVer ) by a version number. For example, version 1.1.0 follows after 1.0.9. If no tag is assigned, the version is automatically tagged with 1.0.0. Tools like flimsy or git hooks shorten this desert of symbols.
8cd852c96ec1e60e8a5ac1f3614b2397
...Unfortunately,MySQL does not offer the ALTER TRIGGER function. To edit an existing trigger, you must first delete it and then regenerate it. The CREATE TRIGGER statement can be read indirectly via the information_schema. This allows us to change triggers indirectly. To do this, make your changes in the result of the following SELECT command (previously change database and trigger name) and execute the query.
...VanillaJS has been virtually on a par with jQuery since ES6 and is now far superior in all areas. this makes it worthwhile to gradually migrate legacy code away from jQuery. however, you have to be careful when triggering manual change events. for example, document.addEventListener does not trigger on jQuery.change(). the following overview summarizes the special features.
...The setting of cookies by your own or third-party scripts can be finely controlled with the help of PHP and JavaScript. Although this is not a sufficient solution for the implementation of cookie solutions after the court ruling against Planet49 (here it is crucial that tracking tools such as Google Analytics do not even track and consequently do not set cookies), it can make sense be to generally whitelist / blacklist cookies.
...In order to save electricity or reduce your own monitoring paranoia, it is advisable to completely disconnect devices that are not in use on your own computer. Devices such as sound boxes or webcams can be deactivated / activated in the classic way via the device manager. The whole thing also works via script. The standard way of doing this used to be devcon . Windows 10 now offers a more convenient way to do this via PowerShell .
...Skype has a nice, somewhat hidden feature: when watching a video broadcast, simply click on the video button and use the"Blurmy background" function to automatically blur the background. Using artificial intelligence, this works with any camera, even without depth information. The whole thing then looks more professional and hides private or for the conversation unimportant things in the background.
...For websites based on WordPress, Joomla or Laravel, for example, which do not have any user-specific content, it is recommended to keep all pages in a static HTML cache and to regenerate the cache manually (or automatically) only when changes are made in the backend. However, if the page contains dynamic content that depends on sessions and cookies or even language and location, the use of OPcache is suitable.
...SVGs play a central role in today's web. not only have they displaced icon fonts, but they also offer the possibility of manipulation via CSS or JavaScript. if you want to save a vector graphic for the web from Adobe Illustrator as SVG, you have to make some settings to avoid pitfalls and reduce loading times, which I will present in the following article.
...Project Euler is a series of exciting programming problems that often have a mathematical background. the problems are often set up in such a way that you have to develop sophisticated algorithms to reach the goal in a reasonable runtime. today we solve problem 15: Lattice paths, where you get to the solution with simple combinatorial means.
...WordPress has implemented background updates natively since version 3.7 and automatically activated them for minor releases. With the help of filters you can control the behavior more precisely what exactly is updated automatically. A permanent, fully automatic installation of all minor, major, plugin, theme and translation updates is not planned, but can easily be done otherwise.
...In order to extend formulas to whole columns within Google Sheets, it is recommended to use the useful function ARRAYFORMULA, which unfortunately does not work in combination with some other important functions like QUERY or INDIRECT, which leaves a complete individual programming of the logic using Google Apps Script or alternatively copying the formula manually down to the last line.
...The Simpson's paradox is one of the easily understandable and at the same time astonishing phenomena in statistics. It occurs whenever groups of data show a particular trend, but that trend is reversed when the groups are combined. With the help of a simple example, the paradox can be understood immediately.
...The Google Tag Manager has established itself as the de facto standard for the integration of tracking scripts. In this way, on the one hand, responsibilities (online marketing vs. programming) are clearly separated and, on the other hand, you can quickly set up and modify tracking via an additional deployment channel. Here are two little tips for setting up triggers.
...From FRITZ! OS 07.10 onwards, if the internet fails, the FRITZ! Box can temporarily use the wireless hotspot of a cell phone as a fallback. The function is hidden under Internet> Access data> Internet provider> Existing access via WLAN . The FRITZ! Box then works as a router itself and provides a network with its own address range. When the Internet is available again, you simply reset the setting. I also had to check the options WLAN> Radio network> 2.4 GHz frequency band active and Internet> Access data> IPv6> IPv6 support active .
...the flower of life is a well-known, flower-like, geometric pattern that has been found in temples, manuscripts and pop culture for thousands of years. the pattern also plays a role in esotericism. we will leave all that aside at this point and concentrate on the simple construction of the geometric form, which is composed of several evenly distributed, overlapping circles.
...Despite all the prophecies of doom surrounding slack and discord, e-mail as an asynchronous communication medium is one of the world's dominant business communication media. In addition to Merlin Mann's Inbox Zero, there are numerous other strategies for dealing with the daily flood of e-mails, including e-mail delaying, i.e. delayed delivery of e-mails.
...For the past few days, I've been studying the following question on StackExchange about a spiral of integers. We are looking for a closed formula for the coordinates of the \(n\) -th element in the following integer spiral, which expands from the origin outwards and further and further into infinity:
.. 9 10 11 12
23 8 1 2 13
22 7 0 3 14
21 6 5 4 15
20 19 18 17 16When working with Google Sheets , fine, user-based rules for editing worksheets, columns and rows can be defined within a spreadsheet. Unfortunately, there is no way to restrict reading rights. However, this would be very helpful in many scenarios. So you only show your customers those tickets that concern them or the employees only the projects they are working on.
...npm is the default package manager for Node.js. Facebook has long been developing an alternative package management solution called Yarn . Yarn seems to be slowly disappearing from the Github readmes as the standard solution and the stats on the official site show that only a fraction of the packages are carried out by Yarn. Nevertheless, it is worth thinking outside the box.
...
The typesetting system \(\TeX\) was developed in 1977 by the legendary Donald E. Knuth, and the software package \(\LaTeX\) is still part of the standard repertoire for creating scientific papers today. The following two tools can be used to convert already generated PDFs as well as handwritten notes into TeX fully automatically. The results are quite promising.
Nick Bostrom's simulation argument is impressively simple and clearly formulated. it doesn't try to prove that we live in a simulation, but instead elegantly formulates three possibilities, one of which must be true. Elon Musk has a similar thesis, which has made the idea known to a broad public. the official paper is already over 14 years old and just as many pages short. yet the central statement is easy to understand and compact.
...the powerful plugins WPML for multilingualism and advanced custom fields for own fields are part of the basic equipment of many installations. it's annoying when malfunctions with data loss occur in interaction. the bug reports on this topic are already several years old and unanswered(here and here and here and here and here). i've taken a closer look at the problem.
...On some Android phones, both the Facebook and Instagram In App browsers (as of today) behave incorrectly if an upload field within an advertised or linked landing page had the accept attribute specified. As a result, the button had no function. If you open the page in the external, normal browser outside of the Facebook app, everything is fine. This is annoying (especially since it has been reported for a long time), but can be solved with a workaround.
...Google Chrome's developer tools are among the most powerful on the browser market. New features pour in every month, which Google presents in compressed form on YouTube . But often it is the little things in life that delight. If you want to delete DOM elements in Google Chrome, you can do this with the delete key. But only today did I notice that DOM elements can also be moved easily using drag & drop:
A golden rule in the git universe is: "Do commit early and often". If the night was a little longer, or if you just want an overview of the current situation on your own computer, the command takes you
d8a38f92d0baa14f9d4568826c13ad46
a "git status" for all repositories that are located in the current folder or in any subfolder and accumulates the values in a nice overview:
In the search for the optimal development environment, Windows 10 offers not only complete solutions such as XAMPP, WAMP and MAMP, a native installation by hand, but also virtualization solutions such as Vagrant(Scotch Box) and Docker(Devil Box, Laradock), but all solutions failed - except for one - due to my requirements such as free configurability, real wildcard SSL certificates, access from all end devices in the local network, and high stability and performance.
...a strength of laravel is the elegant syntax. if you have a lot of models and relations in laravel (due to a lot of tables in the database), traversing can often end up in less elegant code. over the time, three small extensions have proven to be very useful for me, which i want to introduce briefly below. for this purpose, we only use some inheritance, magic methods and custom collections.
...Version management Git is now standard in almost every web project and in every environment (including production). Git always creates the subfolder .git and if this is on the level of the public folder of the website, you can publicly access sensitive files (for example, calling /.git/logs/HEAD shows the last commits) . It explains in detail how you can clone a third-party (!) Git repository without a directory listing.
...in an older blog post i described how to host node.js for free using heroku. now i show a way how to install node.js, npm and composer on any other shared host without root privileges with just a few lines of code. you can install packages, deploy vue.js applications or just start an express.js server. we always work in the user directory and use nvm - the node package manager.
...In PHP <7.2 you can create arrays that can no longer be accessed properly:
91367d1c4636fd753b381406024e303c
You can do some things with it.
...The following command establishes a connection to a server via SSH, executes some commands (for example, changes to a subdirectory and sends a git status ) and leaves the shell open. The .bashrc file is loaded, which enables colored subshells. The trick is to save a temporary file / tmp / initfile with the desired commands, to start a subshell (in our case bash) with the command --init-file. Within this initfile, the same file is deleted again immediately so as not to leave any traces.
...If you integrate a network drive in Windows Explorer, this does not apply system-wide but only for the current user account. This means that you cannot access this network drive in an application that runs with administrator rights. This can be changed easily: Create a new DWORD (32 bit) named EnableLinkedConnections with the value 1 in the registry under HKEY_LOCAL_MACHINE \ SOFTWARE \ Microsoft \ Windows \ CurrentVersion \ Policies \ System and restart. Integrated network drives are then visible everywhere.
...If you want to quickly reach a local folder under Windows that you use again and again, you can simply assign it your own drive letter. There is only a detour via "Connect network drive" because you cannot specify the path C: \ Users \ David \ Downloads, for example. As a solution, enter the so-called administrative share of the drive, which exists by default for every folder: In the above example this would be \\ localhost \ c $ \ Users \ David \ Downloads .
...a frog jumps around on the number ray and you try to catch it. jumping and catching always alternate. the frog starts at position \(s \in \mathbb{Z}\) and at every move it jumps a distance of \(z \in \mathbb{Z}\) (if \(z>0\), it jumps to the right, others if to the left). \(z\ ) is the same at every jump. catching consists of giving an integer position. you don't know \(z\ ) or \(s\ ). we show that there is a way to always catch the frog.
...It is not only when using npm under Windows that you come across a limit that is now almost 30 years old, which limits the paths to folders and files to a maximum of 255 characters. This is not NTFS's fault, but LFN . This leads to annoying bugs and incompatibility between operating systems. In the times of WSL this is a regrettable condition, which luckily you can fix yourself in the registry for some time.
...In the PHP framework Laravel within production environments, workers and supervisors ensure that the jobs stored in, for example, Redis are processed. If you want to be completely independent of this on localhost, you can either use the sync driver to always execute the jobs immediately. This has the disadvantage that the current PHP process is blocked and the request hangs until the job has been processed.
...With the help of the JavaScript library analytics.js from Google Analytics, any events on websites can be tracked. These events are, for example, an exact measurement of the length of stay, the maximum scroll depth of the visitors or other individual actions such as submitting forms. If you want to evaluate advertising campaigns or carry out A / B tests later, for example, you create so-called target projects.
...Server-side rendering is now part of the standard repertoire of websites and applications. even browsers like google chrome tend to cache as much as possible to minimize loading times of further calls. cache invalidation of css/js/image files can be solved with the help of mod_pagespeed, Expires/Cachecontrol header, a cache manifest or very pragmatically and directly by individual parameters behind the file name.
...The provider Bitbucket does not offer (even in the paid tariffs Standard and Premium) the possibility to store SSH keys with write permissions on repository level. Storing your personal SSH key on the production server is not an option, because from there you have access to all other projects you are currently working on. Although there are so-called Access Keys, they only allow read permissions.
...The tools from Sysinternals by Mark Russinovich should not be missing on any Windows computer. If you always want to have the latest version at hand, you can integrate it as a network drive. The command net use s: \\ live.sysinternals.com \ DavWWWRoot on the command line is sufficient (as a normal user). Then nice tools like PsList, PsKill or the Process Explorer are portable on the drive S.
...When outputting calendar weeks on a specific date, you have to be careful in Google Sheets (just like in Microsoft Excel). The function = CALENDAR WEEK (TODAY ()) calculates using the American standard, for which the first day of the year is always assigned to calendar week 1. In Germany this is defined differently: Here the first calendar week is the week from which at least 4 days fall into the new year. In Google Sheets you can solve the problem (in addition to other, exciting alternatives like = SHORTEN ((TODAY () - DATE (YEAR (TODAY () - REST (TODAY () - 2; 7) +3); 1; REST (TODAY ( ) -2; 7) -9)) / 7) and the modified = CALENDAR WEEK (TODAY (); 21) ) easily with the specially designed function = ISOWEEKNUM (TODAY ()) .
...Since Let's Encrypt, encrypted web pages have become standard nowadays. SSL certificates are also indispensable for local development (for example, navigator.geolocation requires SSL encryption locally as well). Since version 58 of Chrome, support for CN (Common Name) has been abandoned and SAN (Subject Alternative Name) has been made mandatory instead. As a result, Chrome suddenly no longer accepts all SSL certificates created in the traditional way.
...Consider two persons \(A\) and \(B\) who do not have the same birthday on the same day and who are \(A\) younger than \(B\). Show: There are exactly two age constellations \(a,b \in \mathbb{N}\) for which holds: \(2\cdot a = b\). We first set \(d \in \mathbb{R}^+\) as the age difference between \(A\) and \(B\) at the birth of \(A\) with \( d = d_0 + d_1 \), \( d_0 \in \mathbb{N}_0, d_1 \in \mathbb{R}, d_1 \in [0;1[\). We now consider any time \(x \in \mathbb{R}^+\) after the birth of \(A\) with \(x = x_0 + x_1\), \(x_0 \in \mathbb{N}_0, x_1 \in \mathbb{R}, x_1 \in [0;1[\).
...Since Git knows that it doesn't know folders, but only files, empty folder structures don't end up in the repository, but since many frameworks and projects require them, they should end up there. A common practice is to create so-called placeholder files (often called .gitkeep) that implicitly specify the folder structure. These files can be easily created and additionally, if desired, make sure that other files in the folders are ignored.
...hosting for node.js is still not very widespread, especially in the german-speaking world. here, the american cloud company heroku offers a remedy - and even for free. you always notice the paradigm "build apps... not infrastructure" and yet you have hardly any restrictions. we implement a small cronjob based on phantomJS as an example, which scans a website every day and sends the page title via email.
...In addition to the diagonal arguments , Georg Cantor also developed the Cantor pairing function \(\mathbb{N}^2 \to \mathbb{W}, \quad c(x,y) = \binom{x+y+1}{2}+x = z\) , which encodes any two numbers \(x,y \in \mathbb{N}\) in a new number \(z \in \mathbb{N}\) . For example, \(c(3,4)=\binom{3+4+1}{2}+3 = \binom{8}{2}+3=\frac{8!}{6!\cdot 2!} +3 = 31 = z\) a unique coding of the numbers \(3\) and \(4\) in the number \(31\) . Show: The set of values \(\mathbb{W} = \mathbb{N}\) , ie \(z\) assumes all natural numbers.
...\(r_1 = 6370km\) at the earth (as a sphere with \(r_1 = 6370km\) ) and a pea (as a sphere with \(r_2 = 2mm\) ) and \(r_2 = 2mm\) a rope over the equator so that it lies tightly on the surface. Now you lengthen both ropes by one meter each. Both ropes should now lie fully extended over the equator again - they no longer lie completely on the surface, but hover over the equator. How high above the surface does the rope float above the earth, how high above the pea?
...In how much % of the time of a day are all three hands of an analogue watch located in the right half of the dial? First of all, the hour hand is located on the right side of the dial in 12 of 24 hours (50%). Of this time, the minute hand is located on the right side in 6 of 12 hours (25%). Of these 6 hours, the second hand spends 3 hours on the right side (12.5%).
...Laravel makes communication with the database a lot easier with Eloquent. When working with Eloquent Relationships you should be aware when calling dynamic variables (with the help of the magic methods of PHP) that the instances of the models do not reflect new changes, but are stored permanently when they are first called.
...There is a hard limit of 2 GB when hosting Git on Bitbucket - if this is exceeded, you only have read-only access to the repository. To prevent this, you can, for example, retroactively remove large folders or files from your commits. But also in other cases (if access data has entered the history or node_modules has slipped back to master) you have to retrospectively manipulate the history of Git, contrary to its nature.
...In the age of Let's Encrypt , encrypted websites are now standard. However, wildcard or extended certificates with particularly trustworthy owner validation are also often required. The provider DomainFactory offers inexpensive SSL certificates that can also be used externally. The setup on a current IIS succeeds without CSR with the help of OpenSSL . In the following I will briefly show which steps are required for this.
...In 1987, Thomas M. Cover posed the following astounding question in "Open Problems in Communication and Computation": Player \(X\) writes two different and randomly chosen natural numbers \(A\) and \(B\) on two different pieces of paper and places them face down on a table. Player \(Y\) now randomly chooses one of these pieces of paper, sees the number and must now decide whether this number is smaller or larger than the other number that is still face down on the table.
...When a soccer game starts, the ball lies in the center of the field and is then moved around the field for 45 minutes by shifting and turning. At the beginning of the second half the ball is again on the center of the field. We show with simple means of linear algebra that either an infinite number of points on the surface are always in exactly the same position as in the original state or exactly 2.
...When debugging blade templates in Laravel 5.*, you often get meaningless error messages referring to cached views. But all of them used to be better: The debugging view in version 4 contained more helpful functions and was also visually more beautiful. With a few lines of code, you can get this functionality back with the help of whoops ("PHP errors for cool kids").
...whether references, partners or customers - there are many cases where you want to display several logos next to each other in a harmonious way. the proportions of the logos are usually not uniform. often you follow your gut feeling when it comes to the size representation in the design, but there is also an exact calculation method of a visually appealing representation by equating the areas of the logos. in the following example, this can be done with a few lines of JavaScript.
...During your daily work with variables in PHP and JavaScript you often come across the query whether a variable is empty. It is worth knowing the native functions and their differences for checking. Annoyingly, there is no simple method to intuitively check whether a variable exists or not. What is meant by this is illustrated in the following matrix. However, small helper functions can be used to retrofit the desired function.
...With sipgate .io S ipgate has created an exciting cloud API which offers a wide range of possibilities around internet telephony. One account is free of charge, and in the Feature Store you can set any free sender number. The documentation of sipgate.io is still expandable, but with a little bit of reading into the official Sipgate API you can quickly realize exciting things.
...Relational database management systems based on SQL are only conditionally suitable for hierarchical or recursive queries. In this case other systems like ArangoDB are better (there was a great talk about this at the GOTO 2016). But you can also create recursive queries in SQL using Common Table Expressions and thus query e.g. classic parent/child tables for all ancestors and descendants.
...According to w3techs.com , around 27.4% of all websites worldwide are currently operated with the help of WordPress. In very many cases, these are not blogs. WordPress automatically generates numerous, often unused URLs and produces so many links indexed by Google that the website operator did not even have on the screen. All of this can be deactivated with a simple command.
...If you get into the predicament of renaming thousands of form field names like I did, you can use the JavaScript console included in Acrobat, where you can not only execute arbitrary JavaScript code, but also access all contents within the PDF (including form fields). Since there is no native renaming function in the JS-API, the form fields are copied with all their properties and created with new names.
...In Shopware 5, a known problem has still not been resolved: If you create an article with mutually dependent variants with mutually exclusive configuration options, it can happen that some combinations cannot be selected in the front end and therefore cannot be ordered. With the help of a plugin, the problem can be easily fixed at the moment.
...There are numerous proofs of the infinity of prime numbers - the well-known theorem of Euclid from the Book of Elements is not missing in any basic lecture on number theory. 2015 Sam Northshield published in the American Mathematical Monthly (issue 122) a no less elegant proof of contradiction in the form of a one-liner, which I do not want to withhold from you (with short comments).
...You can visually enhance the despicable Windows Command Prompt with a few simple steps. You can not only customize the command line in terms of color and size, but also extend its functionality (increase the buffer, install a large set of UNIX tools). Although the command prompt does not come close to PowerShell 6.0 or the new Windows 10 Bash Shell, it can be used for everyday tasks.
...In content management systems, URLs are often not always fixed in advance and are therefore not statically created in advance (as a contribution or menu item), but address objects from the database. Similar to WordPress ( as described here ), it is also possible in Joomla to build dynamic URL structures (independent of the internal alias system). Either JRouter can be used here - or you can use a one-liner in .htaccess.
...Modern browsers can use JavaScript to read and write to the user's clipboard, i.e. they can manipulate it. The underlying technology is already old hat, but it is only recently that more and more attacks (under the name "PasteJacking") have been circulating on the net, which take advantage of this possibility to the disadvantage of the inexperienced user. An implementation in JavaScript is banal.
...Swapping SQL table columns is part of the standard repertoire with MySQL - this is not (yet) supported with PostgreSQL. Although the official wiki devotes its own article to the problem, it does not show any practical solution that also supports views, indices and triggers. The following class does this job (for both MySQL and PostgreSQL) either on the command line - or alternatively directly in Laravel 5.
...If you want to quickly open the command prompt in a folder in Windows Explorer, you right-click (one level up) on the folder and hold down the Shift key and select "Open command prompt here" from the context menu. I just found out another, faster method when you are inside the folder: Here you click into the current folder path, type "cmd" and confirm with Enter.
...If you work with hierarchical categories (taxonomies) in WordPress, you will notice that, on the one hand, the display of the checked categories in the backend is confusing and, on the other hand, posts do not automatically end up in the parent category if they are placed in the child category. Both can be straightened out with just a few lines of code using the powerful hook system (in the form of an action and a filter).
...Besides new features like type hinting for scalar datatypes or the optimized performance, PHP 7 also brings many new, useful language extensions, and finally the "spaceship operator" has made it into the world of PHP (Ruby and Perl programmers have known it for a long time). \($a <=> $b\) returns \(0\) if both operands are equal, \(1\) if the left one is larger and \(-1\) otherwise .
...If you integrate PHP via FastCGI on the IIS 7.5, each script is aborted after 600 seconds (i.e. 10 minutes) by default. A change of the known variable "max_execution_time" in the php.ini has no influence on this, you (also) have to adjust the FastCGI settings. For this, the IIS offers a comfortable interface for managing the relevant variables.
...Conditional probability theory entails beautiful tasks with counterintuitive solutions. In addition to the well-known sibling problem, I will now briefly deal with another example: "I now have two children. One of them is a boy and was born on a Thursday. What is the probability that the other child is also a boy?"
...the file version management system git is slim, fast, and portable. git always handles objects, namely files. folders are only created if there are files in them, otherwise git doesn't capture them in the first place. this has unpleasant side effects in some projects. for example, the shop system shopware relies on strict adherence to the folder structure to function.
...Shopware has a powerful shipping cost module that you can specifically intervene in the calculation. In our case, we want to implement the following scenario: The shipping costs per article are initially determined according to the weight of the article (the weight limits are specified). Only for special exceptions should it be possible to set fixed shipping costs for each item.
...The WordPress permalink system can be adapted very well to your own needs with the help of structure tags . The setting% postname% is probably the most common and practicable solution. However, if you want to implement real dynamic links, you first have to expand the system with your own code.
...One would think that when opening hyperlinks from a Word/Excel document, the default browser would be started with the desired URL, but strangely enough, this is not the case - which leads to unpleasant side effects and makes links for session/cookie-based log-in protected pages in said Office programs impossible.
...On this Father's Day, a daughter gives her father a self-painted picture that her father has long wished for. The daughter says: "I am giving you the picture that you wished for, and my gift will be a surprise". The father trims and reflects on the truth of this statement.
...If you include unencrypted scripts in the <head> area and call up a page with an existing SSL certificate encrypted, these scripts are blocked and therefore not executed. If you simply omit the protocol, all scripts are automatically called in encrypted form if the website is accessed via https: // - otherwise unencrypted.
...When working with multi-dimensional dropdown menus, one often runs into the problem that wrong submenus are opened accidentally or the desired submenu is accidentally closed. This effect occurs when the mouse pointer leaves the corresponding menu at the top level while navigating to an already expanded submenu.
...The following constellation always has an unpleasant side effect: If you protect your site with htaccess / htpasswd and at the same time force an SSL connection, you always need to enter the same password twice (once for http and again after successful entry for https). With the help of the configuration sections introduced in Apache 2.4, the problem can easily be dealt with.
...When programming with JavaScript, you often stumble over the missing possibility to realize multi-line strings by entering them in the code. While the task is no problem in other languages such as PHP or Ruby, JavaScript can only be solved with workarounds, the use of which depends on personal taste and browser support.
...Sending emails with PHP is best implemented with powerful classes such as PHPMailer . Convenient wrapper functions make it possible to use UTF-8 content, embed images and send encrypted attachments with just a few lines of code. If you want to save yourself the overhead and, contrary to the recommendation, use the PHP function mail () , you will run into problems when using umlauts and UTF-8 at the latest.
...Validation tools such as the W3C Markup Validation Service or Google PageSpeed Insights are helpful to objectively evaluate the code and performance of a website. Especially Google influences a whole industry with concepts like above the fold - and also gives strict but useful guidelines in terms of image compression and caching. But it can happen that Google steps on its own feet.
...JavaScript dominates the web - and ECMAScript, the core of the language is growing up. the new specification (ES6 or JS2), which is expected in the middle of this year, brings a lot of new features that you can already try out today. Firefox currently brings the best support, but polyfills through so-called transpilers like Google Traceur are also possible. Below is a short overview of the new features of ES6.
...Whether at school or at university: An interesting question that \( 0,99999... = 1 \) and then includes the question of whether the following equation is true: \( 0,99999... = 1 \) . Although infinity \(0,99999... = A\) in the left part of the equation, we give it a name: \(0,99999... = A\) . After multiplication by the factor \(10\) and simple algebraic transformations, we get a first astonishing insight.
...Just now I was confronted with the following performance problem of a SQL database: In a SQL table called "users" with ~1,000,000 entries, it took an unbearable 28 seconds to determine the number of registrations on today's day. In the "created" column, the times of the registrations were stored in the format "Y-m-d H:i:s".
...Besides the well-known knight problem and queen problem, there are many other exciting questions in the world of chess. I have touched on two small curiosities in a previous blog entry. If you deal with chess problems mathematically, you will soon realize that mathematics provides very simple and enlightening answers to many questions.
...If OneDrive, Dropbox, Google Drive, OwnCloud, box.net: Regardless of the box in which you store your files - the services are almost the same. The clients available for all desktop and mobile systems, the standard unencrypted files and the sharing options differ only marginally. But the OneDrive, which has been integrated into the system since Windows 8.1, has a special feature: only files available online.
...Files on web servers should always be without spaces (not "this is a picture.jpg"), without umlauts or special characters (not "football.jpg"), without backslashes (not "Arbeit \ Auto.jpg") and in lower case (not "" test.JPG "). Recently, however, I had to access and process a large number of files with any file name for a customer project.
...Today I came across the following task while working on a customer project: Take a SQL table "user" with the columns "id" and "score" and determine a ranking of all users sorted by "score", in which users with the same score get the same ranking. By using user-defined variables this task can be solved intuitively and easily.
...When working with the Facebook SDK (more precisely when implementing a Facebook login function within a REST interface), the transmitted token that the client has received from Facebook must first be checked for validity by the server before further operations are performed.
...Whether Chrome, Firefox, Opera, Safari or even Internet Explorer: While well-engineered developer tools were a unique selling point of Firefox and the popular Firebug plug-in until a few years ago, powerful developer tools are now part of the standard scope of every browser in which there is a lot to discover gives.
...I just came across a nice option in MySQL to tap into the file system and obtain valuable information, for example about the existence of files and folders or their contents. This can be very helpful as an alternative to the php function file_exists , since the information about the existence of the file (s) can still be used in the query for further sorting and aggregation functions.
...animated vector backgrounds can bring variety to a web landscape dominated by full-screen photos and videos. it would be nice if loading times as well as broad hardware and software support went hand in hand with this. one solution is called canvas. the JavaScript-controlled HTML element is supported by all current browsers and can be displayed with high performance on mobile devices.
...As a web developer, one is often embarrassed to work with HTML elements that by themselves - in contrast to the img element, for example - have neither a fixed size nor a fixed aspect ratio. Often you want to achieve that these objects behave responsively, but the proportion between width and height is maintained. CSS does not offer an intuitive solution here by default. But with the help of the vertical padding property you can achieve your goal.
...After the Regional Court of Cologne back rowed in the RedTube scandal last week and must never have approved the publication of the disputed IP addresses, it delivers another highly controversial and questionable judgement with its decision 14 O 427/13: The originator of stock photos of a certain picture agency must also be named via the direct access to his pictures via their URL.
...The new features of the HTML5 specification are numerous and many of them are already supported by the majority of the browser landscape - in the following I will highlight an interesting change to the rules for nesting elements. HTML has always distinguished between block and inline elements. For example, the Document Type Definition of HTML4 names h1, p, and div as block elements and a, span, img as inline elements.
...Both Apache on Unix systems and IIS on Windows systems log HTTP requests out-of-the-box in file form. Requests to your own website should not only be evaluated and analyzed manually and automatically (e.g. by log file analyzers such as AWStats) on a regular basis to protect against hacking attacks. The paths of the relevant log files in common configurations are as follows:
/var/log/apache2/access.log(Example: Ubuntu 12.04, Apache 2.2)C:\inetpub\logs\LogFiles\W3SVC1\u_ex<YYMMDD>.log(Example: Windows Server 2012 R2, IIS 8.5)
When integrating Joomla 3.2 on a Windows Server 2008 R2 with IIS 7.5, problems with directory rights often arise, which are often inadequately resolved with settings that are too generously chosen. The following solution is safe and fully functional:
- The group IIS_IUSRS needs the following permissions for C:\inetpub\wwwroot\: read & execute, view folder contents, read, write
- The IIS_IUSRS group needs the rights for C: \ Windows \ Temp \: Read & Execute, Show folder contents, Read, Write
- The user IUSR must be in the group IIS_IUSRS (Computer Management > Local Users and Groups > Groups)
If you need additional special directory permissions for all files uploaded via PHP (e.g. for SSH or FTP), set them also for the folder C:\Windows\Temp\. If you upload a file via PHP, PHP copies this file first into the temporary and then into the final path. If the file ended up in the temporary directory, it inherits its permissions and keeps them after moving it into the final directory.
...In times of the NSA scandal, not only net-savvy users are asking themselves the question of whether and how they can move anonymously on the net to escape the data collection mania of the authorities and secret services. However, this often leads to mistakes and false assumptions. A central misconception is the reduction of anonymity to the concealment of the IP address.
...The discount fitness chain McFIT has given itself a makeover. In the past, a bright yellow mascot in the form of a banana adorned the blue lettering, now a yellow bow on an anthracite-colored background is skilfully looped into one another, thus forming an abstract structure. The FDP colors blue and yellow give way not only to the logo, but also to all other McFIT brand print items.
...When the brothers Thomas and John Knoll started developing Adobe Photoshop in 1987, I was not yet born. Today, in 2013, the software is one of the most popular programs in general and the undisputed market leader in image processing. Thanks to Adobe and the Computer History Museum, the software will now be preserved for posterity in a very special form.
...Chess has fascinated for centuries - its rules are easy to learn and its incredible depth is only accessible to experienced players (of whom I unfortunately do not count). In the following, I will deal with two entertaining questions: Is it possible, by a correct sequence of moves, to reach a position in which the black king is attacked by two white queens at the same time? Is this also possible by two white rooks?
...Movies are usually recorded and played back at 24 frames per second - but the almost 100 year old standard format "24p" seems to wobble. In order to prevent the unpleasant side effects (eg the strong jerking during medium-fast camera pans) of the 24fps projection, work has been done for a long time on doubling the frame rate to 48 frames per second and more.
...Automated spelling and grammar checking is now standard equipment in word processing programs - but checking the spelling of a website automatically has been relatively cumbersome up to now. Google Chrome is taking a first step in this direction with an integrated check in multi-line input fields (textarea). Now there is a service that makes this possible for entire websites.
...Should domain names and email addresses always be lowercase to make sure you get where you want to go? Or is this completely irrelevant? For example, Google's mail servers have curious settings with interesting effects, which I will briefly introduce in the following article.
...I closely follow the design of various programs on German television. Hardly any program retains its corporate design permanently. The evening ritual of the meeting in front of the television screen at 10:15 p.m. on the topics of the day has been causing me stomach ache lately: For some months now, a completely confusing color scheme has been chosen for the presentation of the current stock exchange prices.
...If you optimize your own web presence for mobile devices, you should not only pay attention to different screen sizes, optimized loading times and special features in the operation (such as hover effects), but also to the special capabilities of the devices.
...The same content on different websites is punished by Google in many cases - nevertheless the Google algorithm is intelligent and recognizes whether the elements in the header and footer remain the same or whether entire test passages can be reached twice under different URLs. The exciting question is how Google deals with blog article overview pages.
...The security of the currently most popular content management system WordPress can be significantly increased by turning two small set screws. This requires only 5 minutes and two lines of code. Although the problem can be solved with a variety of plugins, I deliberately limit myself to plugin-free solutions here.
...